OUR SOLUTIONS
Venafi
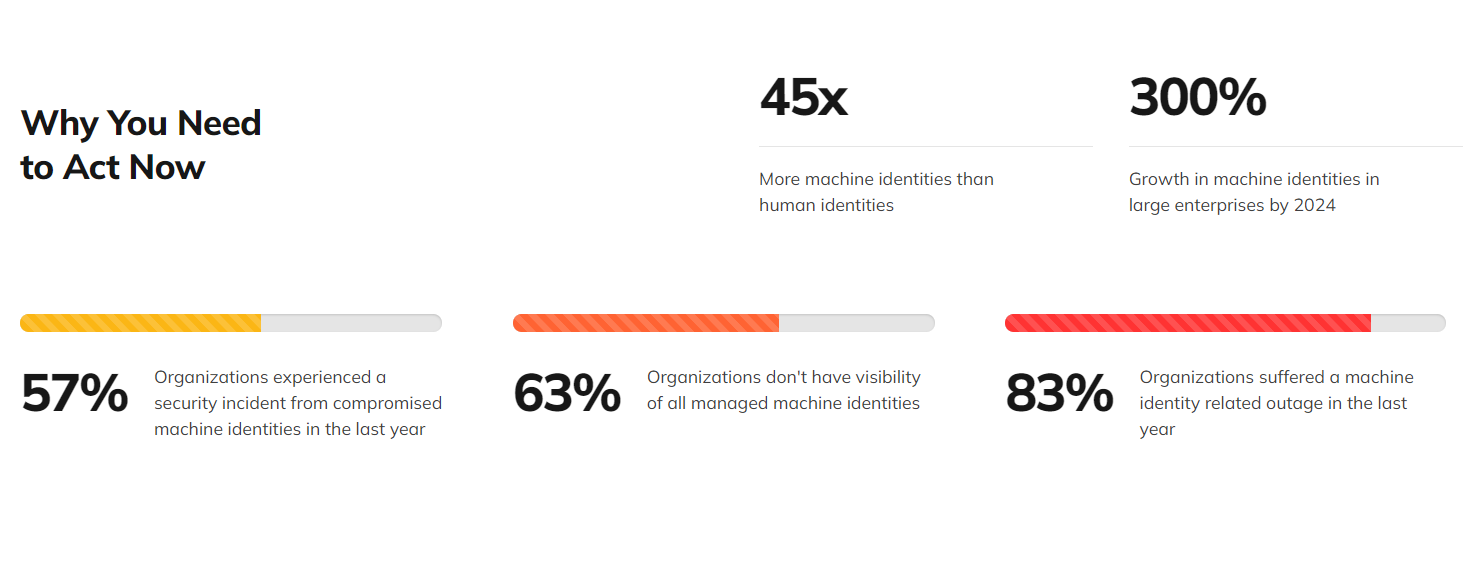
As a result of technological transformations, increasingly widespread and growing systems and security-oriented concerns, manual execution of many operational processes is now a serious challenge for institutions . The most important of these is the management of the life cycles of Digital Certificates . The biggest challenge for institutions is creating a Digital Certificate inventory (which certificates are used in which system), securely storing the private keys and other keys of the certificates (SSH… etc.) , tracking the usage period of the certificates , renewing the ones that are about to expire , transferring the renewed certificates to the target systems. operations such as making it compatible with the certificate , uploading it to the relevant system and terminating the validity of the certificate when necessary. Considering that the validity period of digital certificates produced by Global Authorities is 13 months , all these operations are an effort that is repeated every year . At this point , Venafi provides automation that eliminates all these difficulties for institutions . Venafi is a leading product that provides automation of all processes within the management of the life cycles of Digital Certificates. Venafi also enables systems and devices (servers, applications, cloud services and IoT devices ) to manage their identities and communicate securely with each other and with end users. These identities are typically managed with cryptographic keys and certificates, such as SSL/TLS certificates , SSH keys , and API keys .
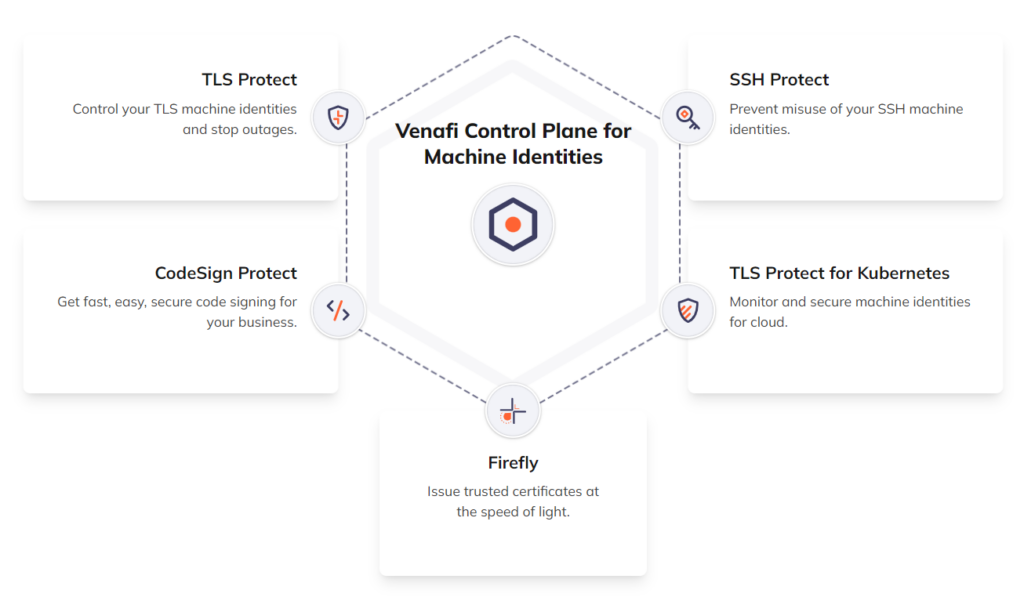
While many automations can be achieved without an agent , an agent may be required for some detailed operations . Venafi both provides automation management and provides automation to different vehicles with the integration of third-party systems . The solutions offered by Venafi are shared below.
Answers
- Venafi Trust Protection Platform : Venafi’s flagship product helps organizations discover, monitor, analyze and protect SSL/TLS certificates , SSH keys and other machine identities . This platform provides a comprehensive solution to meet security and compliance requirements with certificate lifecycle management , policy enforcement and automation features .
- Venafi as a Service : Offered as a cloud-based service , this solution offers organizations a fast and easy way to manage machine identities . Venafi as a Service is especially ideal for small and medium-sized businesses or cloud-focused organizations . This service provides certificate management and automation through a simple user interface .
- Venafi Advanced Key Protect : This product allows organizations to securely manage their cryptographic keys. It is specifically designed for key management and storage that complies with advanced encryption standards.
- Venafi Next-Gen Code Signing : Designed to manage code signing processes safely and efficiently in software development processes. This product is critical to ensuring the integrity and security of the software.
- Venafi Adaptable App Framework : This framework allows organizations to extend and adapt the Venafi platform to fit their specific needs. It provides seamless integration with various applications and services through APIs and integration tools.
- Jetstack by Venafi : Provides security and authentication solutions for Kubernetes and cloud native technologies . Jetstack is a range of products from Venafi for managing Kubernetes and container environments .
These products help organizations ensure security in complex and dynamic IT environments by providing comprehensive support in certificate and key management, security policy enforcement, automation and compliance. Venafi’s solutions are designed to increase network security, simplify management processes and reduce compliance risks.
Key Features
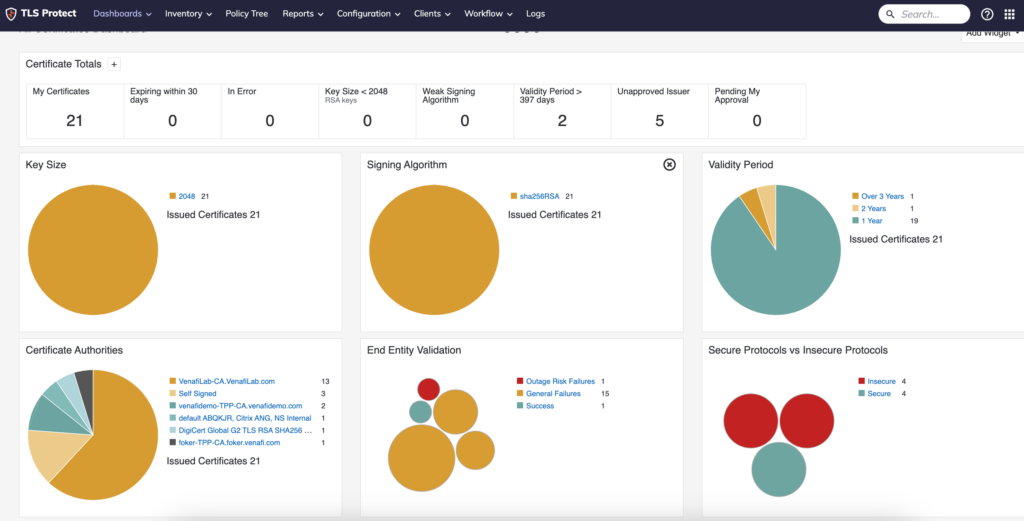
Venafi TrustAuthority and TrustForce are the core components of the platform. TrustAuthority provides the ability to continuously discover and monitor machine identities, while TrustForce provides automatic remediation and verification. These two features increase the security and effectiveness of the platform.
- Automatic Discovery and Monitoring : The platform automatically discovers SSL/TLS certificates and SSH keys on the network. This enables organizations to continuously monitor and manage their existing digital certificates and keys, so vulnerabilities and incompatibilities can be quickly detected.
- Enforcement of Security Policies : Venafi allows organizations to define their own security policies and have these policies automatically applied on all certificates and keys . This helps ensure consistent enforcement of security standards .
- Automation and Integration : Routine tasks such as certificate renewal processes can be automated, reducing workload and preventing human error. Additionally, the Venafi platform can integrate with DevOps tools and cloud services , increasing the efficiency of business processes.
- Reporting and Alerts : Venafi constantly monitors security status and certificate usage . Alerts are sent to system administrators in case of possible security breaches , certificate expirations or policy violations . Additionally, detailed reporting features provide administrators with comprehensive information about the security status .
- Accessibility and User-Friendly Interface : The platform has a user-friendly interface and allows users with different abilities to use it easily thanks to its accessibility features.
- Comprehensive Management of Machine Identities : Venafi can manage various machine identities such as SSL/TLS certificates , SSH keys , and API keys . This facilitates regulatory compliance as well as ensuring network security .
- API and Third Party Integrations : Venafi’s APIs and open source integrations enable easy integration with other security and IT management systems, enabling seamless integration of Venafi solutions into existing infrastructures and workflows.
- Cloud and On-Premise Integrations : The platform is compatible with both cloud and on-premise infrastructures, allowing organizations to flexibly adapt to their existing IT infrastructures .

Usage areas
Venafi Trust Protection Platform’s usage areas are wide and diverse, and it is especially vital for large organizations and companies with complex network structures. The usage areas of the platform are as follows:
- Cyber Security : The platform increases network security by managing SSL/TLS certificates and SSH keys. Strengthens organizations’ cybersecurity posture by continuously monitoring for certificate expirations, incompatible configurations, and potential security breaches.
- Compliance Management : Venafi is used to ensure compliance with various regulatory and industry standards. It is designed to meet compliance requirements for certificate and key management, especially in regulated industries such as finance, healthcare and the public sector.
- Data Center Management : Venafi is used to ensure secure communication between numerous servers and devices in large data centers. The platform ensures that these devices authenticate securely and comply with data encryption standards.
- Cloud Infrastructure Security : Venafi is also vital for the management of cloud-based services and applications. The platform increases cloud security by centralizing the management of certificates and keys used in cloud environments.
- DevOps Processes : In DevOps environments where development and operation processes are combined, Venafi facilitates processes such as automatic certificate renewal and distribution. This allows DevOps teams to develop products faster and more securely.
- IoT Device Management : The certificate and key management required for IoT devices to connect securely to the network and other devices is provided by Venafi. This protects the security of IoT devices and the integrity of the network.
- Third Party Integrations : Venafi can integrate with other security tools and IT management systems. These integrations allow organizations to strengthen and extend their existing security infrastructure.
- Enterprise Risk Management : Organizations can better understand and manage cybersecurity risks thanks to Venafi’s comprehensive monitoring and reporting features. This is used as part of overall risk management strategies.
Integrations
Venafi Trust Protection Platform can work with a wide IT ecosystem by offering a range of integration and add-on options. These integrations enable organizations to seamlessly combine Venafi solutions with their existing security, IT management and business tools. Venafi’s integrations:
- Integration with Cloud Service Providers :
- Amazon Web Services (AWS) : Venafi can integrate with services such as AWS Certificate Manager. This simplifies certificate management for applications and services running on AWS.
- Microsoft Azure : Venafi can integrate with Azure Key Vault and other Azure services, thus centralizing certificate management for applications hosted on Azure.
- Integration with DevOps Tools :
- CI/CD Tools : Venafi can integrate with continuous integration and continuous deployment tools such as Jenkins, GitLab, CircleCI. This integration automates code signing and certificate management processes.
- Container and Orchestration Platforms : Venafi can integrate with Kubernetes, Docker and other container management systems, providing secure certificate management for container-based applications.
- Integration with ITSM Systems
- Demand Management Systems : Venafi can be integrated with demand management systems such as Jira, ServiceNow… etc. and workflows can be created with this integration.
- Integration with Identity and Access Management Systems :
- Active Directory and LDAP : Venafi can manage user authentication and access control processes by integrating with Microsoft Active Directory and LDAP.
- Open Source Projects and API Integrations :
- GitHub and GitLab : Venafi increases security and compliance in software development processes by integrating with open source projects and code repositories.
- RESTful APIs : Venafi’s RESTful APIs can be used to create customized integrations with a variety of applications and services.
- Integration with Security Tools :
- Threat Intelligence and Analysis Tools : Venafi strengthens threat intelligence and event analysis by integrating with security information and event management (SIEM) systems.
- Network Security Tools : Integration with network security tools such as Firewall, IDS/IPS systems helps improve the overall state of network security.
- Integration with Third Party Software and Services :
- Email Security Solutions and Other Business Applications : Venafi can integrate with a variety of third-party software such as email servers and business applications, making certificate and identity management compatible with these systems.
Venafi’s broad integration capacity allows organizations to derive maximum benefit from their existing technology investments , optimize their IT operations and strengthen their security posture . Particularly in the areas of cloud , DevOps and network security , Venafi’s integrations play a critical role in managing the complexities of modern and dynamic IT environments .