OUR SOLUTIONS
Synopsys
Synopsys, Inc. Founded in the USA in 1986, it is a company that produces solutions regarding silicon design and verification, silicon design intellectual property (IP) and quality in the field of Electronic Design Automation (EDA). Products for the semiconductor design and manufacturing industry include tools for logic synthesis and physical design of integrated circuits, simulators and chips for development, and debugging environments that assist in the design of logic for computer systems.
Synopsys Software Integrity Group
Founded in 2016 , Synopsys Software Integrity Group (SIG) is a company that produces Application Security Testing solutions under the Synopsys umbrella. Synopsys Application Security Testing Solutions help build trust and maintain profitability by minimizing business risk throughout the entire software lifecycle (SDLC).
Modern applications are a complex mix of proprietary and open source code, APIs and user interfaces, application behavior, and deployment workflows. Security issues at any point in this software supply chain can put you and your customers at risk. Synopsys solutions help you identify and manage software supply chain risks end-to-end.
Synopsys AST solutions help you develop intelligent, secure, quality products throughout the software development lifecycle

Black Duck Software Composition Analysis (SCA)
Are you using secure open source components? Black Duck Software Composition Analysis (SCA) helps teams select high-quality components and detect open source vulnerabilities in development and production. Black Duck not only exports NTIA-compliant SBOMs, but also enables users to continuously monitor them for newly disclosed threats and problematic components.
Black Duck empowers your development, operations, purchasing and security teams in the areas outlined below:
- Finding and remediating vulnerabilities at every stage of SDLC with detailed, vulnerability-specific remediation guidance and technical insight.
- Eliminating the risk of open source license non-compliance and protecting your intellectual property (including code snippets from larger components) by using the industry’s largest open source knowledge base to determine which of 2,600+ licenses in applications are open source related.
- Preventing development cost overruns and combating code corruption with operational risk metrics associated with poor open source code quality.
- Scanning virtually any software, firmware, and source code to create a comprehensive bill of materials (BOM) of contents.
- Automatically monitor for new vulnerabilities impacting your BOM with custom policies and workflow triggers to accelerate remediation and reduce your risk exposure.
Black Duck Binary Analysis
Do you know what goes into your container images? Black Duck® Binary Analysis gives teams visibility into the content and dependencies of container images so they can address issues before they go into production. With Black Duck Binary Analysis, you can scan a wide range of binary, compression, archive, installation, firmware formats, folder and file images.
Coverity Static Analysis (SAST)
Is your team producing secure code? Coverity Static Analysis (SAST) provides the speed, ease of use, accuracy, compliance with industry standards, and scalability you need to develop high-quality, secure applications. Coverity identifies critical software quality defects and vulnerabilities in code as it is written, early in the development process, when it is least costly and easiest to fix. Precise, actionable fix recommendations and context-specific eLearning help your developers understand how to quickly solve their priority problems without having to be a security expert. Coverity seamlessly integrates automated security testing into your CI/CD pipelines and supports your existing development tools and workflows. With the Code Sight™ integrated development environment (IDE) plug-in used with Coverity, developers can get accurate analytics in their IDE in seconds while writing code. Coverity supports 22 languages and over 70 frameworks and templates.
You can choose where and how to do your development: in the cloud and or on-premises with the Polaris Software Integrity Platform™ (SaaS), a highly scalable, cloud-based application security platform.
In the cloud
With Polaris fAST Static and Polaris fAST SCA, you can add and scan source code and infrastructure-as-code templates in minutes with automatic SAST scans triggered by source code management (SCM) and continuous integration (CI) events.
Within the organization
Software Risk Manager (SRM) integrates the SAST solution into a unified application security posture management (ASPM) solution with centralized policy management, test orchestration, issue prioritization and remediation monitoring.
Integrated development environment (IDE)
With the Code Sight™ IDE plugin, developers can find and fix security issues in real time as they write code. Fast, incremental scans save developers time by flagging vulnerabilities and suggesting fixes directly in the IDE so they can be fixed before returning.
Coverity Static Analysis (SAST)
Do you want to perform security tests of your applications interactively? The Seeker® Interactive Application Security Testing (IAST) solution provides unparalleled visibility into your web application security posture and identifies vulnerability trends against compliance standards (for example, OWASP Top 10, PCI DSS, GDPR, CAPEC, and CWE/SANS Top 25). Seeker enables security teams to identify and track sensitive data, ensuring that it is handled securely and not stored in log files or databases with weak or no encryption.
Unlike other IAST solutions that only identify vulnerabilities, Synopsys Seeker can also determine whether a vulnerability (for example, XSS or SQL injection) can be exploited, providing developers with a risk-prioritized list of verified vulnerabilities in their code to immediately fix. Seeker quickly processes hundreds of thousands of HTTP(S) requests using patented methods, identifying vulnerabilities and reducing false positives to near zero. This allows security teams to focus on actual confirmed vulnerabilities first, greatly increasing productivity and reducing business risk. It’s like having a team of automated penetration testers evaluating your web applications 24/7.
Software Risk Manager (SRM) / Application Security Posture Management (ASPM)
So, how about making Application Security work easier, managing all the tools you use from one place, ensuring accountability, and eliminating silos between tools, processes and teams? Software Risk Manager (SRM) is an Application Security tool that allows security and development teams to manage application security programs on an enterprise scale. It is a Posture Management (ASPM) solution.
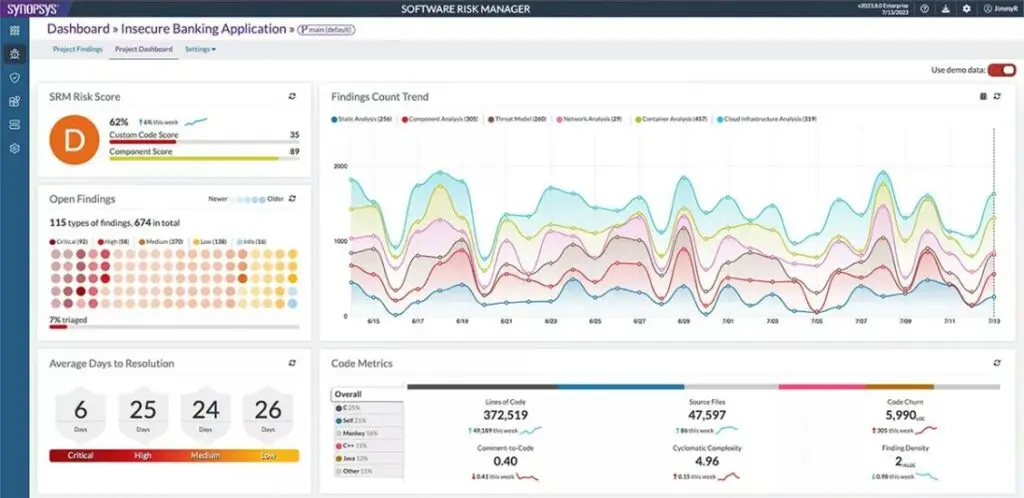
Providing policy-based test management, correlating and prioritizing findings from various tools, SRM is integrated with over 135 third-party software security testing tools. SRM also has the option of using Black Duck SCA and Coverity SAST solutions integrated within SRM. Findings from tools that are not readily available integrated can be included in SRM in .XML format.
Synopsys is a Recognized Leader in Software Security
Synopsys has been named a ‘leader’ by the Gartner® Magic Quadrant for Application Testing for 7 consecutive years , including 2023 . Synopsys is also a Leader in the 2023 Forrester Wave™ in SAST and SCA.

Call Forcerta now for your Application Security Testing Needs. Let us provide you with information about our solutions, demo and organize POC/POV.