OUR SERVICES
ASSESS Risk and Maturity Assessment
Challenges and Risks in Cybersecurity for Companies
In the current landscape, companies are facing increasing challenges and risks in the field of cybersecurity. In this context, through our ASSESS service, we capture a snapshot of companies’ security postures and conduct in-depth analyses to determine their current maturity levels and potential risks. Subsequently, strategies are offered to enhance maturity levels and reduce identified risks. This article will discuss how our ASSESS service can create value for your company.
The Value of ASSESS
- Proactive Approach in Cybersecurity: The ASSESS service adopts a proactive approach in cybersecurity, helping to identify areas for improvement and potential threats and vulnerabilities in advance.
- Risk Reduction, Maturity Enhancement: This service analyzes your current cybersecurity status in technology, people, and processes dimentions, identifies risks, and offers recomendations to minimize these risks. It also provides support for your development areas to enhance your cybersecurity resilience and readiness.
- Customized Security Strategies: Every company has unique needs. ASSESS develops customized security strategies tailored to your company’s specific needs, prioritizing your risks and guiding you along a roadmap customized for your company.
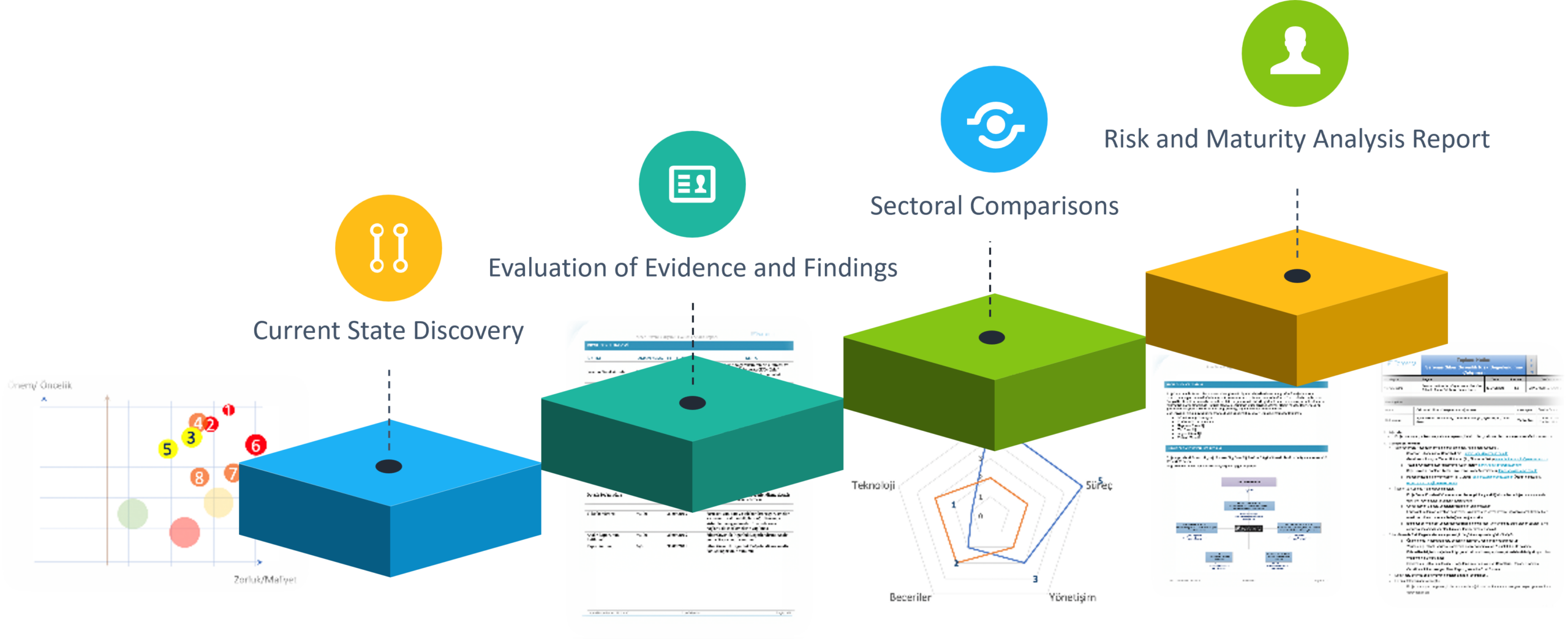
How Does the ASSESS Service Work?
- Current State Assessment and Analysis: As first step, we conduct a comprehensive analysis of your company’s current security state.
- Determining Your Security Risks and Maturity Level: Your current risks and maturity level are identified, and sectoral comparisons are provided.
- Reporting and Recommendations: Based on the analysis results, detailed reports are prepared, and recommendations for improvement are provided.
- Follow-up: After the report, guidance can be provided along the prioritized risk roadmap, or periodic reviews can be done supporting your teams to progress independently.
Advantages of the ASSESS Service
- Strong Cybersecurity Posture: ASSESS helps strengthen your company’s cybersecurity posture.
- Cost-Effectiveness: Effective risk management prevents unnecessary costs and allows for more efficient use of resources.
- Competitive Advantage: A strong cybersecurity posture provides your company with a significant competitive advantage in the market.
Features of the ASSESS Service
- Comprehensive Security Review: ASSESS conducts a detailed security assessment of your company’s entire network structure and applications.
- Expert Team Support: Our expert and experienced teams support you in the security analysis, recommendation and implementation process.
- Continuous Monitoring and Updates: With ASSESS, your security posture is continuously monitored, and necessary updates are recommended.
For Which Companies is ASSESS Service Suitable?
- Large and Medium-Sized Companies: Especially large and medium-sized companies can greatly benefit from the ASSESS service.
- Technology-Focused Companies: Cybersecurity is critically important for technology-focused businesses. ASSESS meets the security needs of these types of businesses.
- Any Company Prioritizing Security: Companies of any size and sector that prioritize security can benefit from the ASSESS service.
Conclusion The ASSESS service offers innovative and effective solutions to the challenges companies face in cybersecurity.
Frequently Asked Questions
- What type of security analysis does the ASSESS service offer? ASSESS thoroughly analyzes your company’s network structure, applications, and security policies to identify potential risks and current maturity level.
- Which types of companies can use this service? Companies of all sizes and sectors can benefit from the ASSESS service, especially technology-focused companies.
- What is the cost of the ASSESS service? The cost of the ASSESS service is customized according to your company’s needs and size. Contact us for detailed information.
- How are security vulnerabilities identified and reported? Depending on the scope, security vulnerabilities are identified through detailed technical analyses and assessments. The findings are presented in understandable and detailed reports.
- How long does the ASSESS service take to complete? The duration of the service varies depending on the size and needs of your company, typically completed within a few weeks.
- Is support provided after the ASSESS service? Depending on the scope, we offer continuous support and consulting services following our ASSESS service.